集時安全技術團隊 ( InTimeSec MDR資安服務) 在監看主機時,發現使用者下載到被 Blackmoon 加料的社交軟體 LINE。
使用者大多習慣從網頁查詢關鍵字而不會留意到點選的網址是購買廣告曝光的釣魚網站。程式執行後會安裝正常的 Line 通訊軟體,但也同時會 Drop 出惡意程式,將惡意程式寫入服務進行常駐,與駭客中繼站進行連線。
駭客入侵手法剖析
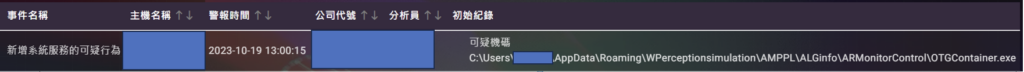
Stage 1 – 告警
分析人員發現有異常程式 (OTGContainer.exe) 寫入服務,在 %UserProfile% \Appdata\Roaming\ 底下。
透過程序樹狀圖反查後會發現 OTGContainer.exe 是透過執行 BBC.exe(7z.exe) 解壓縮所產生。
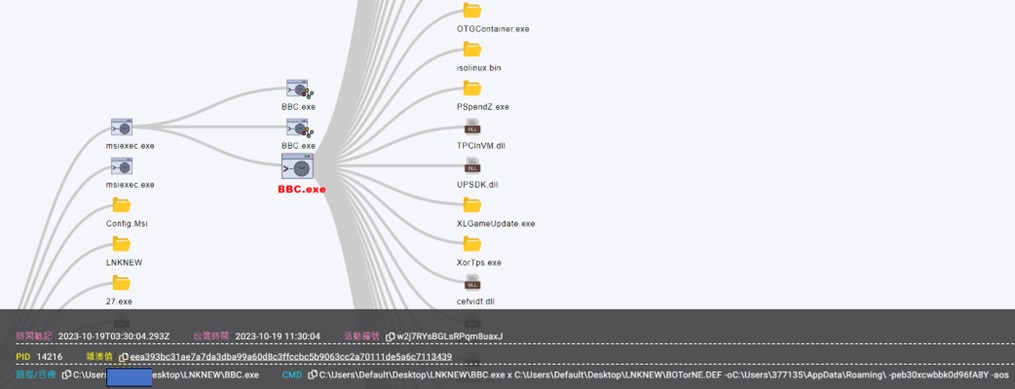
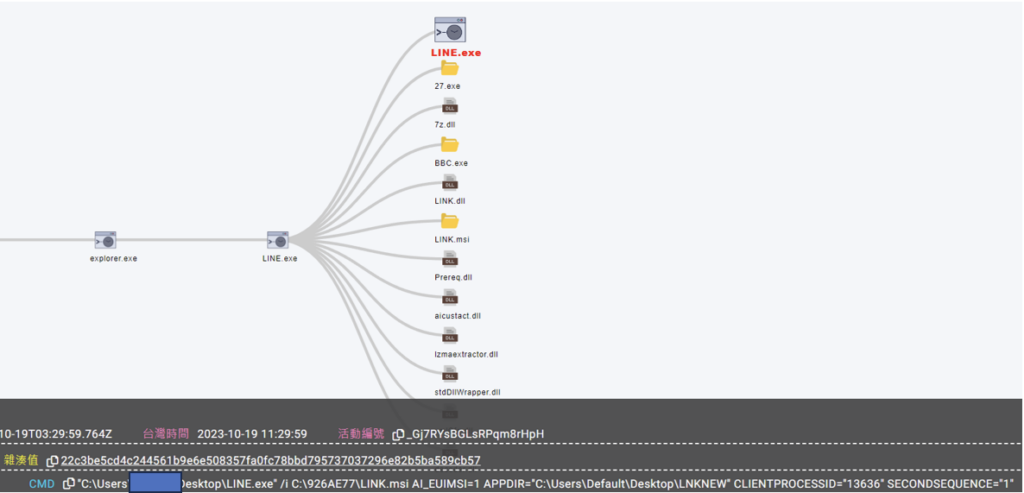
追查 BBC.exe 後發現是使用者執行 LINE.exe 後所產生的相關檔案,LINE.exe 主要帶起 LINK.msi。
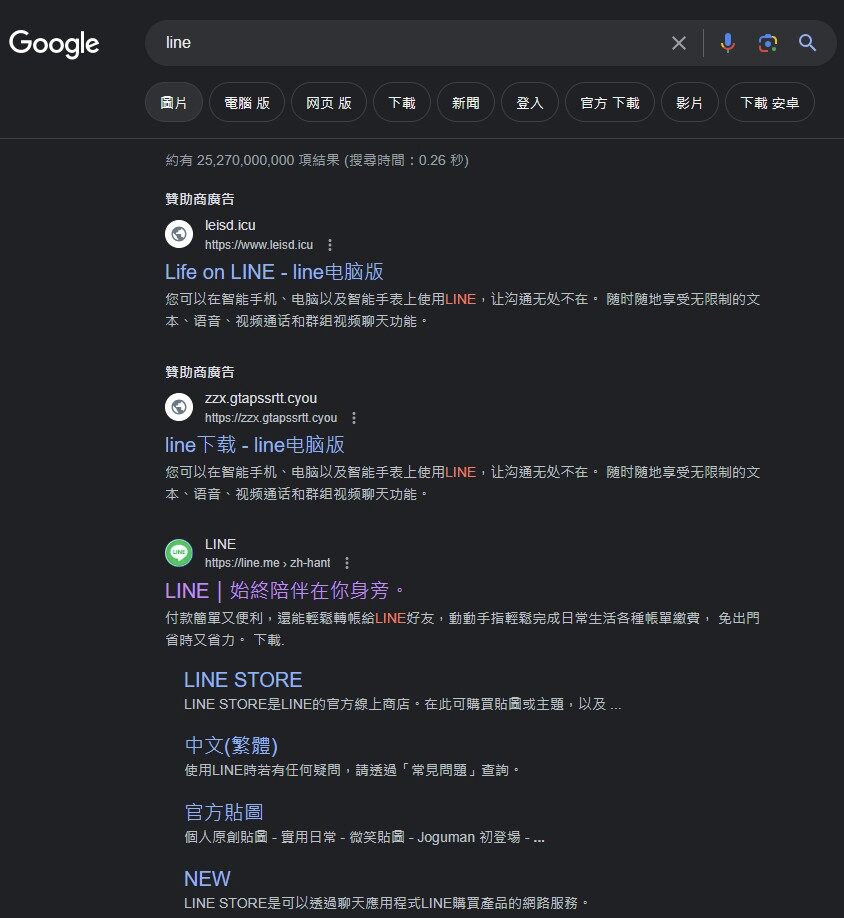
Stage 2 – 源頭
調查源頭後發現駭客透過購買 google 廣告方式,將假的 LINE 通訊軟體網站置頂,誘騙使用者點擊下載加料的 LINE 程式。
Stage 3 – MSI 安裝檔
- LINE.exe 是透過 Advanced Installer [ v15.2.0.0 ] 進行打包。
- 將 LINE.exe extract 出來後主要分為壓縮檔、7Z、MSI。
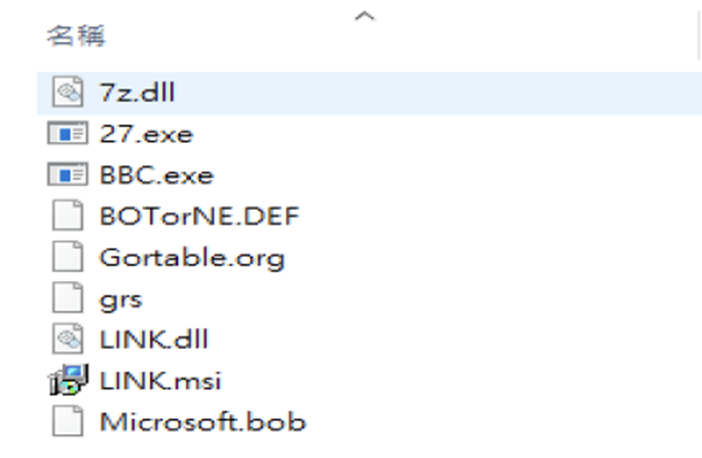
Link.msi 主要是執行 link.dll,將壓縮檔解壓縮至指定路徑,並執行 Bor32-update-flase.exe。
- BOTorNE.DEF : %UserProfile% \Appdata\Roaming\Wperceptionsimulation
- Microsoft.bob : C:\Users\Default\Desktop\LNKNEW\yybob
- Gortable.org : %UserProfile% \Appdata\Roaming\LINEK (正常LINE檔案)
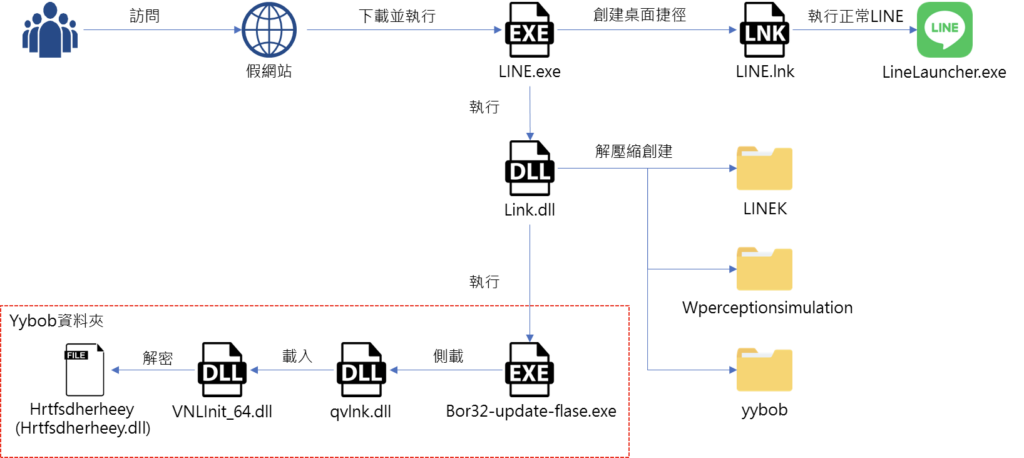
Stage 4 – Payload 解密
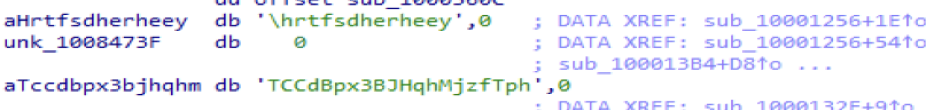
- 所有 payload 均使用 RC4 進行加密,每個 payload 的 key 都不同。
- Loader (VNLInit_64.dll) 對加密 payload (Hrtfsdherheey) 使用 RC4 進行解密,key : TCCdBpx3BJHqhMjzfTph。
Stage 5 – Blackmoon
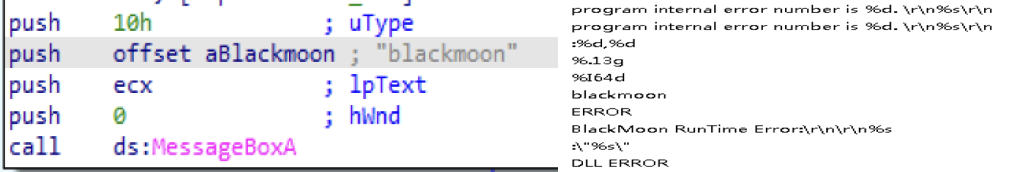
Payload 解密後為一個 dll,可發現 debug 字串特徵 ” blackmoon”。
Stage 6 – 寫入服務
- Hrtfsdherheey.dll 會 drop 出 test.bat,並將 OTGContainer.exe (迅雷遊戲軟體) 寫入服務常駐,執行 Haloonoroff.exe。
- Haloonoroff.exe 會透過側載方式載入 TDPCONTROL.dll,再載入 cefvidf.dll 解密 vnetlib32。
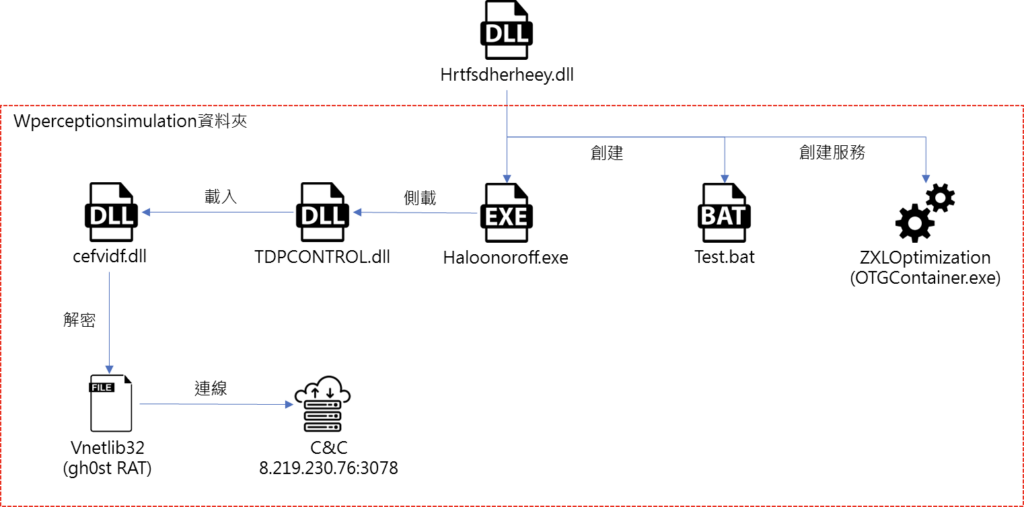
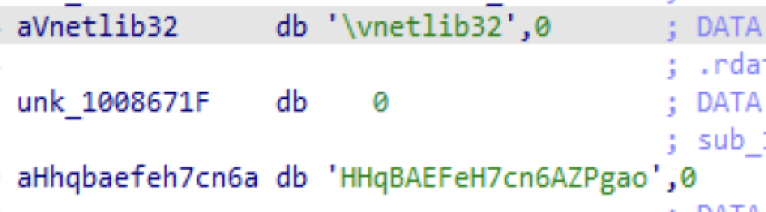
Loader(cefvidf.dll) 對加密 payload (vnetlib32) 使用 RC4 進行解密,key : HHqBAEFeH7cn6AZPgao。
Payload (vnetlib32) 解密後為 gh0st RAT。
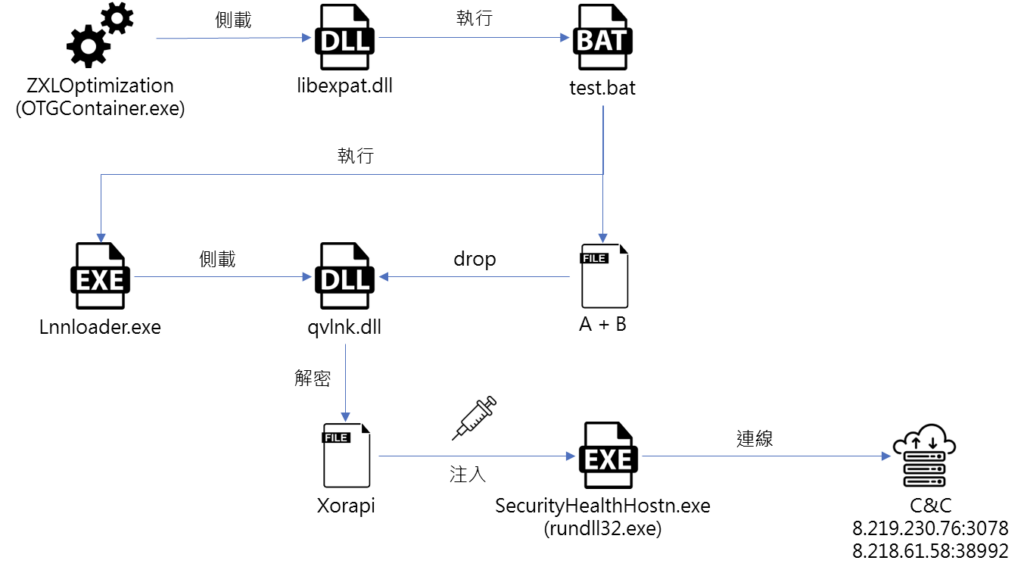
- OTGContainer.exe 會側載 libexpat.dll,libexpat.dll 會去執行先前被 drop 出來的 test.bat。
- Test.bat 會將同路徑下檔案 A 跟 B 結合產生 qvlnk.dll,接著執行 Lnnloader.exe。
- Lnnloader.exe 會側載 qvlnk.dll,讀取 Xorapi 進行解密。
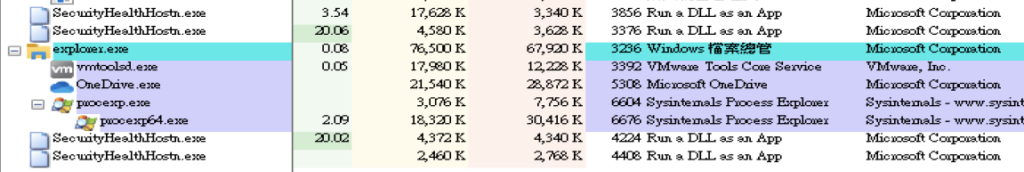
- Xorapi 為 libcef.dll,會 Drop 出 rundll32.exe 到C:\windows\SecurityHealthHostn.exe,並將額外 payload (WGLogin.olg、NULL.bin、Ptuity.plx、Win.rbg) 解密注入 SecurityHealthHostn.exe 記憶體。
Stage 7 – Gh0st RAT
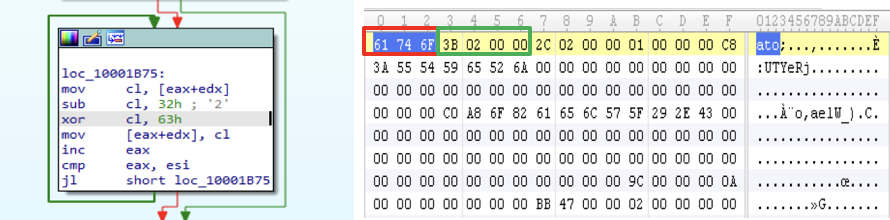
Gh0st config 使用 xor 63h 與 add 32h 進行 decode,讀取同路徑下特定檔案進行 decode,檔名帶有P字樣的檔案為通訊 Port。
- Lost : 8.219.230.76
- LostP : 3078
- LostShe : 8.218.61.58
- LostPShe : 38992
- ComeOn : Line
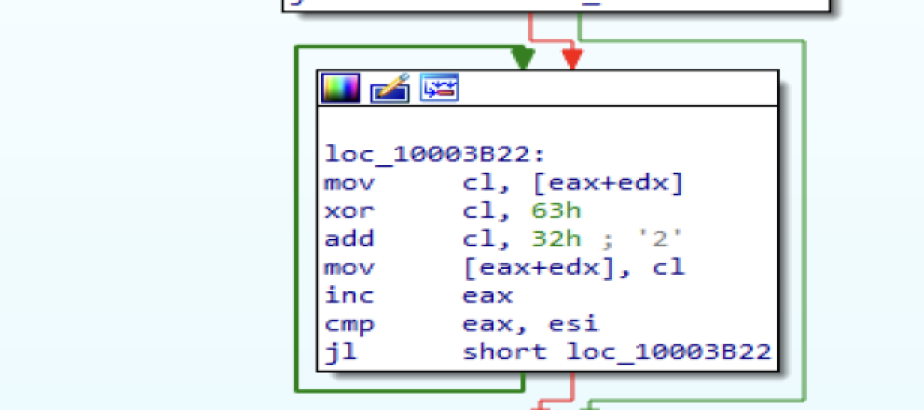
- 封包傳輸使用 sub 32h 與 xor 63h 做 encode。
- Magic header 為 ato(\x61\x74\x6F),加密後為 \x4C\x21\x5E,後面 4 bytes 為封包大小 (\x00\x00\x02\x3B),其餘為資料。
結論
駭客透過加料正常程式及購買註冊假網站,誘騙使用者下載執行惡意程式,透過多種逃避技巧躲避單位現有防護機制,進而埋入後門程式,可竊取單位機敏資訊或造成損失。
InTimeSec MDR 提供專業 7*24 威脅偵測應變 MDR 資安服務 (Managed Detection And Response, MDR),做主動且即時的鑑識調查,讓駭客即便繞過傳統防護機制,還能有異常行為分析在最後一道防線進行阻擋,將單位損失壓縮到最小。
駭客入侵手法整理 MITRE ATT&CK Techniques:
| 策略 | 技巧 | 摘要說明 |
| Resource Development | Acquire Infrastructure: Malvertising(T1583.008) | Hackers purchased online advertisement for a fake Line website published by them to distribute malware (a fake Line installer) |
| Execution | User Execution: Malicious File (T1204.002) | The user executes LINE.exe; and Line.exe subsequently executes Bor32-update-flase.exe |
| Persistence | Create or Modify System Process: Windows Service(T1543.003) | Hrtfsdherheey.dll creates a new service to establish persistence on the target host |
| Privilege Escalation | Executable Installer File Permissions Weakness(T1574.005) | Line.exe turns off UAC’s privilege elevation |
| Defense Evasion | Hijack Execution Flow: DLL Search Order Hijacking(T1574.001) | OTGContainer.exe loads a malicious .dll file – libexpat.dll |
| Defense Evasion | Deobfuscate/Decode Files or Information (T1140) | cefvidf.dll decrypts payload Vnetlib32 |
| Defense Evasion | Process Injection: Dynamic-link Library Injection(T1055.001) | libcef.dll injects into the process of SecurityHealthHostn.exe |
| Command and Control | Encrypted Channel(T1573) | gh0st RAT in the memory can evade detection by encrypted TCP communications |
惡意程式移除清單 IOCs
| Filename | SHA-256 | note |
| LINE.exe | 22c3be5cd4c244561b9e6e508357fa0fc78bbd795737037296e82b5ba589cb57 | MSI installer |
| qvlnk.dll | 540927469495c41abcb9af2ff5428e3c70f494ac4ee89e52495eca48f4fa983e | Blackmoon dll |
| VNLInit_64.dll | 99788859c123dbd52d34505cbcb7fea0f768548dc9eceeb7348f7c50817eaf80 | Blackmoon loader |
| hrtfsdherheey | 70d6181f80e15c638fa2ad641834e705880e86f310296d864d5a05c02cb03f6f | Encrypt Blackmoon dll |
| test.bat | 9153b4aa01053f5cc47cd77a59abeee87efa35e310e702bea56abe71b3fc8044 | Script |
| TDPCONTROL.dll | 413b3e6e3594be89ec548f87e1f45b5dff3b6d08d44488c87cf997462c28f20d | Blackmoon hijack dll |
| vnetlib32 | c0de3305bd078b42c06b14b5cc33984070957233ea9b2d62beb5bc4635e585b7 | Encrypt gh0st RAT |
| Xorapi | 67a91bfcc0540f3e48c104a42bd511a2792bd4f44c5d5749d53a7b2379fee3e5 | Encrypt Blackmoon dll |
| libexpat.dll | dc3aee991887a033417199b46f9feb4c9f285d11e33f9207b3bd84ecdb906b96 | Blackmoon dll |
| WGLogin.olg | cb5342fb7a3f98f61aa079d8e77396a546c204a14fdc98ac8400d127f941d0b5 | Encrypt gh0st RAT |
| NULL.bin | 50ccb2b2ad7a709df2a548ec1000a945646814f03dd60952d361557f3f9be7bb | Encrypt gh0st RAT |
| Ptuity.plx | e0b322fdb9e1421c48ea7def682e7b431b4b34225592a1eca47573bdd03befc9 | Encrypt gh0st RAT |
| Win.rbg | 0e0ecf143040929969166ca5db4ae9f55d60a5c2146287686bfbd78ef4ff0259 | Encrypt gh0st RAT |
| 8.219.230.76 | C&C server | |
| 8.218.61.58 | C&C server |


